The Payment Card Industry (PCI) Security Standards Council (SSC) has finally released the long-awaited update to the Data Security Standard (DSS) – and it’s a big one! Increasing from 139 pages to 380 pages, this fresh release is full of information.
DSS v4.0 replaces v3.2.1 to address emerging and evolving risks and technologies, and to provide innovative ways to combat new threats and achieve compliance. You can find and review the updated standard and Summary of Changes on the PCI SSC website.
These updates are intended to satisfy the payment industry’s increasing security needs; promote security as a continuous process; and expand flexibility, while also establishing a process to answer the industry’s demands for a customized approach to achieving compliance.
While the newly released standard is available for validations starting Q3 2022, version 3.2.1 continues to be available for validations until March 31, 2024.
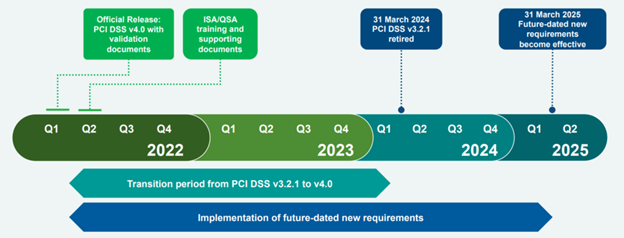
Image from the PCI DSS 4.0
What’s New with PCI DSS 4.0?
A More Customized Approach to Security Controls and Compliance Auditing
The biggest buzz around DSS 4.0 is the new “customized approach” to achieving compliance. Previously, a business had to conform to the defined process that was the DSS. The SSC now offers a structured customized approach, which will allow more flexibility to businesses as they undergo PCI validation.
Rather than the previous approach of making companies complete specific, prescriptive requirements in their entirety, this new method focuses more on achieving the end goal of each requirement. As far as getting there? Organizations are now allowed to implement controls that make the most sense in their environment.
Not only do merchants gain more flexibility on their own security controls; their audit process becomes more flexible as well. With a customized validation, there are no written testing procedures for assessors to follow. Instead, your assessor will develop proper testing processes to validate that your security controls achieve the objective of the DSS. This new unique approach appears to recognize and address the fact that PCI compliance is no longer a one-size-fits-all concept.
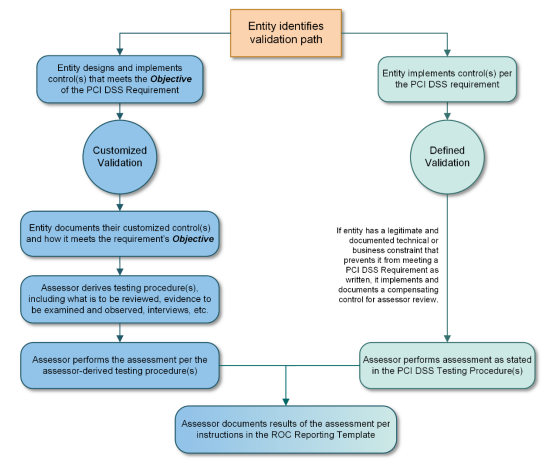
Image from the PCI DSS 4.0
60 New PCI Compliance Requirements
In addition to this new approach to compliance, there are more than 60 new requirements in version 4.0. While that’s a lot of change, most of these requirements will remain “best practices” until 2025, when they will be promoted to requirements. Companies can use this grace period to create, implement, and test these new controls and to establish their roadmap towards complying with the new elements of the standard prior to those requirements becoming mandatory. Merchants are encouraged to take advantage of this grace period.
It’s also important to note that the 12 core PCI DSS requirements did not fundamentally change from V3.0 to V4.0. In fact, most of the changes included in this release are clarifications or enhancements. Where there was ambiguity or “wiggle room” in the previous release, the SSC added clarity to many existing requirements, enhancing the intention behind the requirement. This is a good move, as we know that most of a QSA’s job is subjective. Clarifying the requirements simplifies the challenge of remaining on the same page as your QSA.
Clarifications
Over the years since releasing version 3 (and the subsequent minor updates), the SSC has patiently been listening to and collecting feedback from merchants, QSAs, and other third parties. This has allowed them to strengthen the standards and close gaps. The feedback has been used to provide the more defined requirements you’ll find in version 4.0.
An excellent example of this kind of change: the timeframes referred to throughout the DSS.
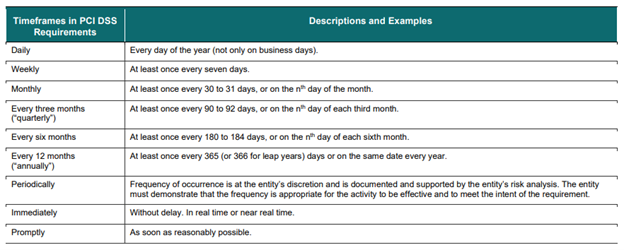
Image from the PCI DSS 4.0
Time requirements have been given an overhaul in DSS 4.0. This version introduces quantifiable definitions for formerly subjective terms like “Periodically” or “Immediately”.
Not only did the PCI SSC enhance the definition of the terms, but they are also using these terms more frequently.
“Periodically” is the best example. Used 9 times in version 3.2.1, we see the term “periodically” in version 4.0 40 times. DSS 4.0 defines periodically as “Frequency of occurrence is at the entity’s discretion and is documented and supported by the entity’s risk analysis. The entity must demonstrate that the frequency is appropriate for the activity to be effective and to meet the intent of the requirement.”
This is interesting because the time period is subjective, with the potential to differ with each validation. The burden lies with the organization being validated to perform regular risk analyses to determine, and later justify, what time period best applies for the DSS’s use of the term throughout the standard. This is another brilliant move on the SSC’s part, enforcing their desire to deploy security as a continuous process within organizations.
Another interesting clarification here is the clarity around the DSS’ use of “Immediately”. It is clear now that any use of the term “Immediately” demands “near-real-time” action. Not first thing tomorrow morning. Not a few hours later. Right now. Immediately. “Promptly” on the other hand, is clearly defined as “As soon as reasonably possible.”
Requirement Changes
When updates were more substantial than just a “clarification”, they were primarily aimed at accounting for new technologies, such as e-commerce, and emerging threats, such as phishing.
Some examples of structural impacts that exceed clarifications are:
- Multi-factor authentication is now required for all remote access to a CDE system (Requirement 8.4.2)
- Password requirements have been updated. (Requirement 8.6.3)
- New standards have been implemented to address phishing and other modern e-commerce attacks
- Disk-level encryption will no longer be an acceptable control for the protection of cardholder data (Requirement 3.5.1.2)
- Internal vulnerability scans must be performed using authentication credentials. (Requirement 11.3.1.2)
- Service provider scope validation must be conducted every 6 months and after any significant changes. (Requirement 12.5.2.1)
You can view a comprehensive summary of changes – both enhancements and clarifications – on the PCI website.
Like the whole of PCI DSS 4.0, most of the major updates are future-dated to give everyone sufficient time to plan and implement the required changes.
What’s Next with PCI Compliance?
If PCI follows their previous patterns, we should expect to see an update to DSS 4.0 sometime around March of 2023.
Generally, PCI will collect feedback immediately following a release in order to update anything egregious within the first year. Additionally, we typically see subsequent updates roll out to all of the Self-Assessment Questionnaires (SAQs). These too will be future-dated, and the existing versions will continue to be validated against for some foreseeable amount of time.
Not quite sure what these changes mean for your business? The best place to start is always with your Qualified Security Assessor. They can provide tailored PCI compliance advice for you to consider.
However, if you’re looking to reduce the overall scope of your PCI compliance requirements, Curbstone is here to help. We understand how complex these requirements – and the corresponding audits – can be; we’re here to make them less of a burden. To find out how our payment processing technologies can take your existing infrastructure out of scope for PCI compliance, contact us today:
This article is provided for general informational purposes only and does not constitute legal advice. If you have questions about your specific compliance requirements, please consult with your PCI-certified Qualified Security Assessor (QSA).

