Earlier this year, Verizon released their 2021 Data Breach Investigations Report. They analyzed more than 79,000 international data breaches from the previous year – and the results provided several interesting insights.
What caused the most data breaches in 2020?
85 percent of breaches involved a human element.
Social engineering* was responsible for the most breaches – followed closely by basic web application attacks and system intrusion. Fewer than 10 percent of breaches were caused by the misuse of privileges (e.g., an employee accessing a database that they did not have permission to access.)
*The report defines “social engineering” as the “psychological compromise of a person, which alters their behavior into taking action or breaching confidentiality.” This also includes unintentional actions – such as clicking on a link in a phishing scam.
Lost and stolen assets
Lost and stolen assets accounted for 1,295 incidents – 84 of which resulted in confirmed data disclosure.
While most people think of lost computers or cell phones, lost and misplaced documents also fall into this category. For instance, if a merchant were to write a customer’s credit card number on a piece of paper and this document were later lost, this incident would be considered a lost or stolen asset. While lost devices are slightly more common, lost documents (and other types of physical media), account for 43 percent of lost and stolen asset incidents.
What types of data were the most valuable targets?
Credentials (e.g., usernames and passwords) were by far the most commonly targeted type of data. Personal data, such as names and addresses, and healthcare data took the second- and third-place spots.
For the last several years, Verizon’s researchers have found that payment card data has become a less frequent target overall – although in several specific industries, it was the first or second most sought-after type of data.
- In retail, 42 percent of incidents targeted payment card data
- In accommodations and food service, 33 percent of incidents targeted payment card data
- In manufacturing, 19 percent of incidents targeted payment card data
Even though personal information and healthcare data have drawn some of the attention away from credit card data, financial information still remains the most popular data being shared on criminal marketplaces. In an analysis of terms that appeared most frequently on criminal forums, bank was – by far – the most common. Others included:
- Bank identification number
- Card
- CVV
- VISA
- Bank account
- Account number
What industries experienced the most breaches overall?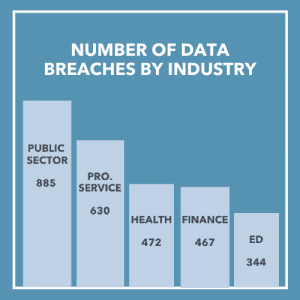
Without taking data type into account, the industries that experienced the most breaches – as well as the most total incidents – were:
- Public sector
- Professional, scientific, and technical services
- Healthcare
- Finance
- Education
What does this mean for your business?
Whether you’re a small business or a large enterprise, cybersecurity must be taken seriously. With the median financial loss associated with a data breach coming in at $30,000 – and the largest coming in at over $985,000 – a single incident can come at a considerable cost (not to mention the reputational damage that can occur in the aftermath.)
It’s crucial to protect all of the sensitive data that your customers entrust you with – from contact information to credit card numbers – but you don’t have to do it alone. At Curbstone, we can help you secure your customers’ payment data from today’s most common threats. Our payment processing software moves sensitive data off your system, where it would otherwise remain vulnerable to ransomware, malware, and other attacks. As a PCI-validated Level I Service Provider, we maintain the highest level of security controls required to maintain compliance – and we complete annual third-party security audits so you don’t have to. You can qualify for a shorter, less time-consuming PCI self-assessment questionnaire, without sacrificing the security of your customers’ data.
To learn more about the ways Curbstone can help you better protect your organization from payment card data breaches, contact us today.

